------------------------------------------------------------------------------------------------
Explanation:
if n=0, then DFA should accept only epsilon .....
total 2 states are reuired for n=0
if n=1, then DFA should accept { a,b}
total 3 states are reuired for n=1
if n=2, then DFA should accept { aa,ab,ba,bb}
total 4 states are reuired for n=2
Answer: 4 bits
Answer: Logical
Explanation
Answer: All of the above
Answer: (a) Timeout
Explanation :
DB2 allows you to put a limit on the amount of time you’ll wait at a database level using the LOCKTIMEOUT configuration parameter.
Answer: C
Explanation:
Both are declarative ( http://en.wikipedia.org/wiki/Declarative_programming )
Answer(b) (u,v)>=12, using Floyd Warshall algorithm
Progress Requirement: If no process is executing in its critical section and there exist some processes that wishes to enter their critical section, then the selection of the processes that will enter the critical section next cannot be postponed indefinitely.
Answer: (a) presentation layer
Explanation:
Layer 6:Presentation Layer
The presentation layer presents the data into a uniform format and masks the difference of data format between two dissimilar systems. It also translates the data from application to the network format. Presentation layer is also responsible for the protocol conversion, encryption, decryption and data compression. Presentation layer is a best layer for cryptography.
Network Devices: Gateway Redirector is operates on the presentation layer
(1) ∃x∀y Q(x,y)
(2) ∀x∃y Q(x,y)
Explanation:
(89) Consider unsigned integer representation. How many bits will be required to store a decimal number containing 3 digits
tags:
net solved papers computer science, net computer science question paper , ugc net computer science solved papers, free net solved papers computer science, net computer science study material, net computer science books, net computer science syllabus, net solved papers for computer science, net solved papers 2005, net solved papers free download, June 2005 solved paper,apset 2012, apset previous question papers, apset computer science question papers, previous question papers,apset previous question papers,apset previous question papers 2012, apset previous question papers 2011, previous question papers of apset, apset syllabus, apset syllabus 2012, apset syllabus 2012 paper 1, syllabus for apset 2012, apset computer science model papers, apset computer science material, apset syllabus for computer science, ugc net answer key, ugc net ans key,ugc net answer key 2012,ugc net june 2012 answer key, Ugc net key 2012, Answer key of ugc net june 2012
Net June 2012 Computer science and applicationts Question paper with solutions
( UGC Net answer key for June 24, 2012 )
--------------------------------------------------------------------------------------
(1) Granulairity refers to
( UGC Net answer key for June 24, 2012 )
--------------------------------------------------------------------------------------
(1) Granulairity refers to
(a) Size of a database
(b) Size of a data item
(c) Size of a record
(d) .........
Answer: (a) size of a data item
(2) R = (A, B, C, D). We decompose it into R1 = (A, B), R2 = (C, D). The set of
functional dependencies is: A → B, C → D, Then decomposition is a
(a) Dependency preserving but lossy
(b)Dependency preserving and lossless
(c) lossless
(d) Neither lossy nor dependency preserving
Answer: (b) Dependency preserving but lossy
(3) if A(x) = {0.1,0.2,0.3, .....}
B(x) = {0.3,0.4,0.5,......}
then find out Complement of A ∩ B
Solution:
(1)find out Intersection first using below rule
Standard intersection (A ∩ B)(x) = min [A(x), B(x)]
(2) Find out complement using complement rule
Standard complement cA(x) = 1 − A(x)
(4) Find out which of the following grammer is in GNF(Greibach Normal Form )
Options: given 4 grammers and we need to find out the grammers which are in GNF
(5) Find out the Regular expression produced by the following DFA
(a) b(b*+a*b)
(b) a*b(b*+aa*b)*
Answer: (B)
(6) (1) Every context-sensitive language is recursive
(2) There exist recursive languages that are not context-sensitive
which of the following are correct statements
(a) (1) only
(b) (2) only
(c) Both (1) and (2)
(d) Neither (1) nor (2)
Answer: (C)
Explanation:
Every regular language is context-free, every context-free language is context-sensitive
and every context-sensitive language is recursive and every recursive language is
recursively enumerable. These are all proper inclusions, meaning that there exist
recursively enumerable languages which are not recursive, recursive languages that are
not context-sensitive, context-sensitive languages which are not context-free and contextfree languages which are not regular.
(7) One Question on the closure properties of Recursively enumarable languages, Recursive languages and context free languages
Closure properties
Recursively enumerable languages are closed under the following operations. That is, if L and P are two recursively enumerable languages, then the following languages are recursively enumerable as well:
- the Kleene star
 of L
of L - the concatenation
 of L and P
of L and P - the union

- the intersection

Note that recursively enumerable languages are not closed under set difference or complementation. The set difference L - P may or may not be recursively enumerable. If L is recursively enumerable, then the complement of L is recursively enumerable if and only if L is also recursive.
Recursive languages are closed under the following operations. That is, if L and P are two recursive languages, then the following languages are recursive as well:
- The Kleene star

- The image φ(L) under an e-free homomorphism φ
- The concatenation

- The union

- The intersection

- The complement of

- The set difference

The last property follows from the fact that the set difference can be expressed in terms of intersection and complement.
Closure properties
Context-free languages are closed under the following operations. That is, if L and P are context-free languages, the following languages are context-free as well:
- the union
 of L and P
of L and P - the reversal of L
- the concatenation
 of L and P
of L and P - the Kleene star
 of L
of L - the image
 of L under a homomorphism
of L under a homomorphism 
- the image
 of L under an inverse homomorphism
of L under an inverse homomorphism 
- the cyclic shift of L (the language
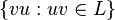 )
)
Context-free languages are not closed under complement, intersection, or difference. However, if L is a context-free language and D is a regular language then both their intersection  and their difference
and their difference  are context-free languages.
are context-free languages.
 and their difference
and their difference  are context-free languages.
are context-free languages.[edit]Nonclosure under intersection and complement
The context-free languages are not closed under intersection. This can be seen by taking the languages  and
and  , which are both context-free. Their intersection is
, which are both context-free. Their intersection is 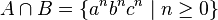 , which can be shown to be non-context-free by the pumping lemma for context-free languages.
, which can be shown to be non-context-free by the pumping lemma for context-free languages.
 and
and  , which are both context-free. Their intersection is
, which are both context-free. Their intersection is 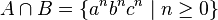 , which can be shown to be non-context-free by the pumping lemma for context-free languages.
, which can be shown to be non-context-free by the pumping lemma for context-free languages.
Context-free languages are also not closed under complementation, as for any languages A and B:  .
.
 .
.Closure properties
The regular languages are closed under the various operations, that is, if the languages K and L are regular, so is the result of the following operations:
- the set theoretic Boolean operations: union
 , intersection
, intersection  , and complement
, and complement  . From this also difference
. From this also difference  follows.
follows. - the regular operations: union
 , concatenation
, concatenation  , and Kleene star
, and Kleene star  .
. - the trio operations: string homomorphism, inverse string homomorphism, and intersection with regular languages. As a consequence they are closed under arbitrary finite state transductions, like quotient
 with a regular language. Even more, regular languages are closed under quotients with arbitrary languages: If L is regular then L/K is regular for any K.
with a regular language. Even more, regular languages are closed under quotients with arbitrary languages: If L is regular then L/K is regular for any K. - the reverse (or mirror image)
 .
.
(8) (1) Deterministic and non-deterministic DFA's are equivalent
(2) Deterministic and non-deterministic PDA's are equivalent
which of the following are correct statements
(a) (1) only
(b) (2) only
(c) Both (1) and (2)
(d) Neither (1) nor (2)
Answer: (A)
(9)
which of the above graphs are planar.
Options
(a) G1 only
(b) G2 only
(c) Both G1 and G2
(d) Neither G1 nor G2
Answer (b)
Explanation:
Graph G2 is planar because we can redraw the same graph with out any crossovers.
Explanation:
Graph G2 is planar because we can redraw the same graph with out any crossovers.
(10) (a+b) (a+b) (a+b) ..... (a+b) n times ... minimum number of states required to implement using DFA
Options:
(a) n (b) n+1 (c) n+2 (d) None
Answer: (c)
Explanation:
if n=0, then DFA should accept only epsilon .....
if n=1, then DFA should accept { a,b}
total 3 states are reuired for n=1
if n=2, then DFA should accept { aa,ab,ba,bb}
total 4 states are reuired for n=2
(11) Length of the IPV4 header field
Answer: 4 bits
(12) Transaction manager functionality is
(13) Match the following
OLAP Datawarehouse
OLTP RDBMS
...............................
(14) Which of the trees needs to have all leaves in the same level
Answer: B trees
(15) which of the following tree gives sorted list during traversal
Answer: BST (Binary Search Tree )
(16) two questions from software validation and verification...
- Software verification asks the question, "Are we building the product right?"; that is, does the software conform to its specification.
- Software validation asks the question, "Are we building the right product?"; that is, is the software doing what the user really requires.
(17) CMM level 4 also included in
(a) CMM Level 2
(b) CMM level 3
(c) CMM level 5
(d) none
Answer: (C)
(18) A grammer has given ... four grammers given as four options . we need to find the equivalent grammer to the given grammer
(19)On a disk with 1000 cylinders, numbers 0 to 999, compute the number of tracks
(20) Question on Amdahl's law on parallel processing
It is often advised to focus system design on hardware scalability rather than on capacity. It is typically cheaper to add a new node to a system in order to achieve improved performance than to partake in performance tuning to improve the capacity that each node can handle. But this approach can have diminishing returns (as discussed in performance engineering). For example: suppose 70% of a program can be sped up if parallelized and run on multiple CPUs instead of one. If is the fraction of a calculation that is sequential, and
is the fraction of a calculation that is sequential, and  is the fraction that can be parallelized, the maximum speedup that can be achieved by using P processors is given according to Amdahl's Law:
is the fraction that can be parallelized, the maximum speedup that can be achieved by using P processors is given according to Amdahl's Law:  . Substituting the value for this example, using 4 processors we get
. Substituting the value for this example, using 4 processors we get 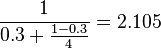 . If we double the compute power to 8 processors we get
. If we double the compute power to 8 processors we get  . Doubling the processing power has only improved the speedup by roughly one-fifth. If the whole problem was parallelizable, we would, of course, expect the speed up to double also. Therefore, throwing in more hardware is not necessarily the optimal approach.
. Doubling the processing power has only improved the speedup by roughly one-fifth. If the whole problem was parallelizable, we would, of course, expect the speed up to double also. Therefore, throwing in more hardware is not necessarily the optimal approach.
(21) java.util.*
Match the following
Calendar getTimeZone()
Random getNumber()
Timezone setId()
...................
I think...
Random getNumber()
(a) CMM Level 2
(b) CMM level 3
(c) CMM level 5
(d) none
Answer: (C)
(18) A grammer has given ... four grammers given as four options . we need to find the equivalent grammer to the given grammer
(19)On a disk with 1000 cylinders, numbers 0 to 999, compute the number of tracks
the disk arm must move to satisfy all the
requests in the disk queue. Assume the
last request serviced was at track 345 and
the head is moving toward track 0.The
queue in FIFO order contains requests for
the following tracks :
123,874,692,475,105,376.Perform the
computation for SCAN scheduling
algorithm :
Answer: 1219
(20) Question on Amdahl's law on parallel processing
It is often advised to focus system design on hardware scalability rather than on capacity. It is typically cheaper to add a new node to a system in order to achieve improved performance than to partake in performance tuning to improve the capacity that each node can handle. But this approach can have diminishing returns (as discussed in performance engineering). For example: suppose 70% of a program can be sped up if parallelized and run on multiple CPUs instead of one. If
 is the fraction of a calculation that is sequential, and
is the fraction of a calculation that is sequential, and  is the fraction that can be parallelized, the maximum speedup that can be achieved by using P processors is given according to Amdahl's Law:
is the fraction that can be parallelized, the maximum speedup that can be achieved by using P processors is given according to Amdahl's Law:  . Substituting the value for this example, using 4 processors we get
. Substituting the value for this example, using 4 processors we get 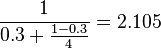 . If we double the compute power to 8 processors we get
. If we double the compute power to 8 processors we get  . Doubling the processing power has only improved the speedup by roughly one-fifth. If the whole problem was parallelizable, we would, of course, expect the speed up to double also. Therefore, throwing in more hardware is not necessarily the optimal approach.
. Doubling the processing power has only improved the speedup by roughly one-fifth. If the whole problem was parallelizable, we would, of course, expect the speed up to double also. Therefore, throwing in more hardware is not necessarily the optimal approach.
(21) java.util.*
Match the following
Calendar getTimeZone()
Random getNumber()
Timezone setId()
...................
I think...
Random getNumber()
.......................................
(22) level of abstraction, describes what data are stored in database
(a) view
(b) abstraction
(c) physical
(d) logical
Answer: Logical
Explanation
The are three levels of abstraction:
- Physical level: The lowest level of abstraction describes how data are stored.
- Logical level: The next higher level of abstraction, describes what data are stored in database and what relationship among those data.
- View level: The highest level of abstraction describes only part of entire database.
(23) hiding data and code ..........
Answer: Encapsulation
(24) Which of the following is linear data type
(a) Strings (b) lists (c) Queues (d) All the above
Answer: All of the above
(25) optimal binary search tree if probability of successful and unsuccessful search are same
(26) Computational Complexity for graph coloring problem
(27) Deadlock is
(a) Timeout
(b) Timein
(c) Both a and b
(d)None
Answer: (a) Timeout
Explanation :
DB2 allows you to put a limit on the amount of time you’ll wait at a database level using the LOCKTIMEOUT configuration parameter.
(28) Software is
(a) schedule with in the budget ....
(29)A common property of logic programming languages and functional languages is:
(a) both are procedural languages
(b) both are based on λ-calculus
(c) both are declarative
(d) both use Horn-clauses
(a) both are procedural languages
(b) both are based on λ-calculus
(c) both are declarative
(d) both use Horn-clauses
Answer: C
Explanation:
Both are declarative ( http://en.wikipedia.org/wiki/Declarative_programming )
(30) A* Algorithm ..heauristic function = g+h ......................
....................................................
(a) g=0 (b) g=1
(c)h=0 (d) h=1
(31) Question on GPS ( GLOBAL POSITIONING SYSTEM )
(32) In unit testing of a module, it is found for a set of test data, at the maximum 90% of the code alone were tested with the probability of success 0.9. the reliability of the module is
a. Atleast greater than 0.9
b. Equal to 0.9
c. Atmost 0.81
d. Atleast 1/0.81
a. Atleast greater than 0.9
b. Equal to 0.9
c. Atmost 0.81
d. Atleast 1/0.81
Answer: (C)
(33) which of the following software metric does not depend on programming language
(a) LOC ( Lines of code )
(b) Function Point
(c) member of token
(d) None
(34) Reliability of a software depend on
(a) Number of errors present
(35) There is an edge between u and v.. (u,v). shortest path from s to u is 53 and shortest path from s to v is 65 then what can you say about (u,v)
(a) (u,v) =12
(b) (u,v) >= 12
(c) (u,v) <=12
(d) (u,v) > 12
Answer(b) (u,v)>=12, using Floyd Warshall algorithm
(36) which of the following is not UNIX shell
(a) Bourne Shell
(b) C Shell
(c) Net Shell
(d) Korne Shell
Answer: (c) Net Shell
(37) CTRL+C Unix .....
(a) user mode
(b) kernel mode
(c) super user mode
(38) two lines .....
(a) Histogram
(b) covariance
....................
...............
(39) Printf("%c",100)
Answer: Ascii values corresponds to 100 ( that is d )
(40) Match the following
Microcontroller 8051
..............................
..............................
(41) Match the following
Instructions addressing modes
..........................................................
...........................................................
(42) Match the following
Regular languages DFA
CSL LBA
CFL PDA
Recursive languages Turing Machine
(43) Question on Prolog ... If --else
(44) Pipeline processing .....
instruction decoding .... instruction execution ....
(45) Microcomputer consits of
(a) perpherials
(b)Micro processor
(c)
(46) Color magneta ............
Red and white
Red and black
(47) In pre-emtive scheduling algorithm if time quantum increases, effective turn around time
Answer: I think Decreases
(48) making capabilities
(a) Conditional transfer
(b) Unconditional transfer
(49) non-sharable resources
(a) Mutual exclusion
...............
.............
(50) if an integer takes 2 bytes.. what is the maximum value can be represented
(51) interrupts
(a) software
(b) Hardware
(c) internal
(d) External
(52) Relationship among claases and objects .... can be represented
(a) class diagram
(b) Object diagram
(53) Which of the following deletes the structure of the data
(a) Erase
(b) Delete
(c) ZAP
(d) Pack
reference: http://msdn.microsoft.com/en-US/library/00c5e99f(v=vs.80)
Command:Visual Studio 2005: Removes all records from a table, leaving just the table structure.
(b) Delete
(c) ZAP
(d) Pack
reference: http://msdn.microsoft.com/en-US/library/00c5e99f(v=vs.80)
Command:Visual Studio 2005: Removes all records from a table, leaving just the table structure.
(54) when one transaction updates a database item and then
the transaction fails for some reason is called
the transaction fails for some reason is called
(a) Dirty read problem
(b) temporary update problem
(55) amplification, modulation and ....................
(56) Number of binary trees with 5 nodes
(57) Given post order traversal ... need find out the preorder traversal\
(58) Consider the methods used by processes P1 and P2 for accessing their critical sections whenever needed, as given below. The initial values of shared boolean variables S1 and S2 are randomly assigned.
Method Used by P1 while (S1 == S2) ; Critica1 Section S1 = S2; Method Used by P2 while (S1 == S2) ; Critica1 Section S2 = not (S1);
Which one of the following statements describes the properties achieved? (GATE CS 2010)
(A) Mutual exclusion but not progress
(B) Progress but not mutual exclusion
(C) Neither mutual exclusion nor progress
(D) Both mutual exclusion and progress
(A) Mutual exclusion but not progress
(B) Progress but not mutual exclusion
(C) Neither mutual exclusion nor progress
(D) Both mutual exclusion and progress
Progress Requirement: If no process is executing in its critical section and there exist some processes that wishes to enter their critical section, then the selection of the processes that will enter the critical section next cannot be postponed indefinitely.
(59) if virtual address space and logical address space is same then
(60) cache memory and interleaved memory
(61) compiler generates window programming
(a) text file
(b) binary file
(c) obj file
(62) Virtual switching and packet switching
(63) base class derived class... constructor order
(64) additions done in computer
(a) CPU
(b) Memory
(c)
(65) Connect different LANS with different technologies
(a) Bridges
(b) switches
(66) Encryption and Decryption of data is done in which layer?
Answer: (a) presentation layer
Explanation:
Layer 6:Presentation Layer
The presentation layer presents the data into a uniform format and masks the difference of data format between two dissimilar systems. It also translates the data from application to the network format. Presentation layer is also responsible for the protocol conversion, encryption, decryption and data compression. Presentation layer is a best layer for cryptography.
Network Devices: Gateway Redirector is operates on the presentation layer
(67)
What is the output for above circuit
option (a) is correct
(68)
K=0;
for i=1 to n
for i1=1 to i
for i2=1 to i1
................
..........
.............
for im=1 to im-1
k=k+1
output for this program?
Answer: C(n+m-1,m)
example:
#include<stdio.h>
main()
{
int k=0;
int i,i1,i2,i3,i4,i5,n=3,m=2;
for (i1=1;i1<=n;i1++)
for(i2=1;i2<=i1;i2++)
k=k+1;
printf("Values of n= %d, m=%d, k=%d",n,m,k);
}
output:
Values of n= 3, m=2, k=6
if we consider option(a) as answer then
c(n+m-1,m)=c(3+2-1,2)=c(4,2)=6
if we consider option(b) as answer then
c(n-m+1,m)=c(3-2+1,2)=c(2,2)=1
So Option(a) is correct.
example:
#include<stdio.h>
main()
{
int k=0;
int i,i1,i2,i3,i4,i5,n=3,m=2;
for (i1=1;i1<=n;i1++)
for(i2=1;i2<=i1;i2++)
k=k+1;
printf("Values of n= %d, m=%d, k=%d",n,m,k);
}
output:
Values of n= 3, m=2, k=6
if we consider option(a) as answer then
c(n+m-1,m)=c(3+2-1,2)=c(4,2)=6
if we consider option(b) as answer then
c(n-m+1,m)=c(3-2+1,2)=c(2,2)=1
So Option(a) is correct.
(69) E-commerce cannot be used in
(a) House banking
(b) for evaluating employee performance
(c).......
...........
(70) if virtual address space is equal to physical address space then ...
(71) Question on COSETS
(72) How many relations are there on a set with n elements that are
symmetric and How many relations are there on a set with n elements that are reflexive and symmetric ?
Solution:
Let R be the set with n elements. Then RxR has n^2 elements in it, and the relationson R correspond exactly to the subsets of RxR, giving us 2^(n^2) relations in general.
If the relation is symmetric, we can think of it slightly differently. Let P2(R) be all subsets of R with 2 elements, and P1(R) be all the subsets of R with a single element. Then all symmetric relations will correspond exactly to the subsets of P2(R) U P1(R). Notice that P2(R) is exactly like RxR, except the pairs aren't ordered, and it only considers pairs with distinct x and y (the pairs where they aren't distinct are covered by P1(R)). How many elements does P2(R) have in it? Well, we are looking for all pairs of the form:
{x, y}
where x and y are distinct and in R. They correspond to an unordered selection of 2 objects from n objects, giving us:
n C 2 = (1/2)n(n - 1)
How many elements of P1(R) are there? Well, clearly, there will be n elements. So, the total number of elements in P2(R) U P1(R) will be:
(1/2)n(n - 1) + n
= (1/2)n[(n - 1) + 2]
= (1/2)n(n + 1)
And, we want the number of subsets of this, so we get:
2^[(1/2)n(n + 1)]
As for all relations that are antisymmetric, that's a bit more tricky. I'll have to think about that one. The relations that are neither reflexive nor irreflexive are not too difficult to count. Assuming that n > 0, it's impossible for a relation to be simultaneously reflexive and irreflexive, so if we count the number of reflexive relations, and the number of irreflexive relations, then we will not have counted the same relation twice, and we can just subtract this number from 2^(n^2).
In both the reflexive and irreflexive cases, essentially membership in the relation is decided for all pairs of the form {x, x}. This leaves n^2 - n pairs to decide, giving us, in each case:
2^(n^2 - n)
choices of relation. That is the number of reflexive relations, and also the number of irreflexive relations. The number of relations that are either reflexive or irreflexive will be the sum:
2^(n^2 - n) + 2^(n^2 - n) = 2^(n^2 - n + 1)
If we subtract this from the total number of relations, 2^(n^2), then we get the number of relations that are neither reflexive or irreflexive:
2^(n^2) - 2^(n^2 - n + 1)
Hope that helps!
EDIT: (Fixed a small mistake previously)
OK, I've just thought of a way to deal with the antisymmetric case. Again, we will consider P2(R) U P1(R). We can choose freely which pairs of the form (x, x) we want in our relation, so we can choose freely our subset of P1(R), giving us 2^n possible contributions from P1(R). As for our contribution from P2(R), for each {x, y} pair in P2(R), we must have exactly one of the following three possibilities:
1) Neither (x, y) nor (y, x) is in our relation.
2) Only (x, y) is in our relation.
3) Only (y, x) is in our relation.
Each choice for each {x, y} can be made independently of the other choices chosen previously. Also, making two distinct choices will result in two distinct relations, i.e. we are not counting anything twice. Therefore, the number of contributions from P2(R) will be:
3^(n C 2) = 3^[(1/2)n(n - 1)]
The contributions of P2(R) and P1(R) are independent, so the total number of antisymmetric relations will be:
2^n * 3^[(1/2)n(n - 1)]
(73) Which data structure is used when you do the post order traversal
answer: stack
(74) what would be the top of elements in stack when u do post order traversal
23^8/23*
Answeer: 6,1
(75) which class of network provides multicasting
Answer: class D
(76) ICMP protocol presents in ------
Answer: network layer
(77) x.25 is
(a) connection oriented
(b) connection less
(c) both
(d) neither of them
Answer : (a)
Answer : (a)
(78)HTML standard
(a) ISO 8879
(79) if an instruction takes i nano seconds ... if it takes extra j nano seconds for every k instructions then effective access time is
Answer: i+j/k
(80) if Q(x,y) represents x+y=0 and x,y are real numbers then
(2) ∀x∃y Q(x,y)
which of the statements are true
Explanation:
Compare these two sentences: "For all x, there exists at least one y such that Q(x,y)" and "there is at least one y such that, for all x, Q(x,y)". Here Q(x,y) is some sentence about x and y, such as "x+y=0". The first of these means that for all x, there is a y WHICH IS ALLOWED TO VARY WITH EACH x which makes Q(x,y) true. So, for example, "for all x, there exists at least one y such that x+y=0" is true because y=-x makes it true.
that means ∀x∃y Q(x,y) is true
The sentence "there is at least one x such that, for all y, Q(x,y)" means that there exists one x which does the job for all y of making Q(x,y) true. This is a much tougher statement to make true! Notice that "there is at least one x such that, for all y, x+y=0" is false for the real numbers---there x has to be -y and must vary with y which this sentence does not allow.
that means ∃x∀y Q(x,y) is false
(81) which of the following is preferable in software
Answer : High cohesion and low coupling
(82) link state algorithm
(83) 1000 ms then frequency
(a) 1 KHZ (b) 10 khz
(84) 10 base Tx
(85) which data structure is used for heirarchical
Answer is Tree
(86) Compare B+ tree with normal trees.. why do we use B+trees
(87) which logic family is fastest
Answer: ECL
Explanation:
ECL (http://en.wikipedia.org/wiki/Emitter-coupled_logic)
(88) To connect diffrent technology networks
Answer: bridge
Answer: ECL
Explanation:
ECL (http://en.wikipedia.org/wiki/Emitter-coupled_logic)
(88) To connect diffrent technology networks
Answer: bridge
(89) Consider unsigned integer representation. How many bits will be required to store a decimal number containing 3 digits
Answer: 10 bits
Explanation:
Ans: O(n*m^n)
(92)consider the declaration Base *b = new Derived;
the order of execution of base and derived class constructors?
Explanation:
we have to find the lowest power of 2 that is higher than that range.
For instance, 3 decimal digits -> 10^3 = 1000 possible numbers so you have to find the lowest power of 2 that is higher than 1000, which in this case is 2^10 = 1024 (10 bits).
(90)Computational Complexity for graph coloring problem
Explanation:
http://www.scribd.com/doc/22874034/A-Notes-on-Design-Analysis-of-Algorithm
(91)Planner graphs can be _____________colored problems
(91)Planner graphs can be _____________colored problems
(a) 2 b)3 c) 4 d) 5
ANS: By the four color theorem, every planar graph can be 4-colored
ANS: By the four color theorem, every planar graph can be 4-colored
Explanation: http://en.wikipedia.org/wiki/Graph_coloring
(92)consider the declaration Base *b = new Derived;
the order of execution of base and derived class constructors?
a) derived class constructor followed by base class
b) base class constructor followed by derived class
*****************************************************************************
Tags:
UGC NET Solved Sample Question Paper, ugc net solved question papers June 2012, Key to ugc net solved question papers June 2012, ugc net guide, ugc net papers, ugc net, ugc india, ugc payscale, ugc 6th pay comission, ugc pay revission, ugc syllabus, ugc exam, ugc result, ugc pay calculator, ugc india, ugc india website, ugc india new pay scale, ugc education, ugc net result, ugc net 2009, ugc net 2008, ugc net result, ugc net question papers, ugc net december 2008, ugc net june 2008 result, ugc net application form, ugc net result, ugc net application, ugc net in computer science, ugc net in indiatags:
net solved papers computer science, net computer science question paper , ugc net computer science solved papers, free net solved papers computer science, net computer science study material, net computer science books, net computer science syllabus, net solved papers for computer science, net solved papers 2005, net solved papers free download, June 2005 solved paper,apset 2012, apset previous question papers, apset computer science question papers, previous question papers,apset previous question papers,apset previous question papers 2012, apset previous question papers 2011, previous question papers of apset, apset syllabus, apset syllabus 2012, apset syllabus 2012 paper 1, syllabus for apset 2012, apset computer science model papers, apset computer science material, apset syllabus for computer science, ugc net answer key, ugc net ans key,ugc net answer key 2012,ugc net june 2012 answer key, Ugc net key 2012, Answer key of ugc net june 2012








super bossu nee memory !!!
ReplyDeletethanks... may be ee week lo expect cheyyachu
Deletehave u applied for apset?
Deleteno haven't ??
Deletei saw some post in one of the groups in FB
apset ante deniki - can u pls tell me
APSET is like NET exam but apset is only andhra... syllabus is exactly same as NET syllabus...
Deletefor more info
apset.org
Thanks bhanu
DeleteKey publish eppudu avutundi
ReplyDeletedo u have any idea ?
and whr will it be ?
---lakshmi
may be ee week lo vundachu.
Deletecan u pls let me know once these are out ?
Deletelakshmipathi.j@gmail.com
very nice sir.
ReplyDeleteWelcome Ashwini.. How was ur exam
DeleteHow is : (10) (a+b) (a+b) (a+b) ..... (a+b) n times ... minimum number of states required to implement using DFA
ReplyDeleteOptions:
(a) n (b) n+1 (c) n+2 (d) None
Answer: (c), I think it should be (b)
We need n+2 states because n states are required for n length string and 1 state for initial and 1 dead state.. So total n+2 states.. Willl add state diagram in the blog soon
Deletei have edited my blog.. added few diagrams
DeleteHello...
ReplyDeleteVery good work...thank a lot..
In question 9 G2 can not be planar graph...its of type k3,3 so i can'b be planar.
http://en.wikipedia.org/wiki/Planar_graph
Thanks for the complement....
DeleteGraph G2 is planar because we can redraw the graph without any crossovers ..
I have added the new graph in my blog. please check...
Do not hesitate to discuss on any questions provided in my blog.
HI GREAT WORK... BUT ARE ALL THE QUESTIONS FROM PAPER III?
ReplyDeleteHi deepali. Most of the questions are from paper-3 but not all
Deletehave u any more question on paper 3
ReplyDeleteHi,
DeleteI have added as many questions as possible by using my memory.. i do not have any more.. if i can recollect then i will to this post.
Please let me know if you remember any questions....
Thanks
Great work sir!
ReplyDeleteI would like to suggest some modifications!
A common property of logic programming languages and functional languages is:
ANS: both are declarative ( http://en.wikipedia.org/wiki/Declarative_programming )
which logic family is fastest
Answer: ECL(http://en.wikipedia.org/wiki/Emitter-coupled_logic)
Thanks ravindra... i checked the wiki and you are right.. i will update answers accordingly..
DeletePlease check other questions and answers if you have time , let me know if you find any mistakes...
let me know if you remember any questions from paper-2 and paper-3...
bhanu.
Which of the following deletes the structure of the data
Delete(a) Erase
(b) Delete
(c) ZAP
(d) Pack
reference: http://msdn.microsoft.com/en-US/library/00c5e99f(v=vs.80)
Command:Visual Studio 2005: Removes all records from a table, leaving just the table structure.
i think this question is related to DBMS (SQL commands)... What do you say ravi
Deleteif it is related to SQL -oracle then truncate or drop should be there.
Deletei am guessing that this question is not from oracle - SQL.
(56) Number of binary trees with 5 nodes
Delete(a) 32 (b) 36 (c) 120 (d)42
answ: 42
reference: http://theory.cs.uvic.ca/inf/tree/BinaryTrees.html
Hi Ravi, how many marks you are expecting in paper-3?
Deleteno Yaar, I was confused while writing exam..! i lost 7 known questions and i could not attempt 1 or 2 questions.
Deletei just getting answers for available questions with your help.
i am expecting 30 to 34 questions as per key available in internet. i need 34 questions to qualify.
let us hope positive!
1. Computational Complexity for graph coloring problem
ReplyDeleteAns: O(n*m^n) (http://www.scribd.com/doc/22874034/A-Notes-on-Design-Analysis-of-Algorithm )
2. Planner graphs can be _____________colored problems
a) 2 b)3 c) 4 d) 5 (options like that)
ANS: By the four color theorem, every planar graph can be 4-colored(http://en.wikipedia.org
/wiki/Graph_coloring)
3. consider the declaration Base *b = new Derived;
the order of execution of base and derived class constructors?
a) derived class constructor followed by base class
b) base class constructor followed by derived class
(like that)
Thanks ravi.....
Deletegud work guys
ReplyDeleteThanks buddy.....
Deletehi bhanu garu ? how many question has correct answers in ur paper 3 key?
ReplyDeleteHi sunil. I am expecting around 37-42 are correct. Have you applied for apset?
Deleteyes i applied.WHERE R U FROM? DO u FIND ANOTHER CS PAPER3 KEY WHICH IS PUBLISHED IN THE INTERNET? wat about ur opinion on that key?WAT IS UR EXPECTATION IN THAT KEY?
ReplyDeleteMy native place is guntakal.. but working as associate professor in one of the engineering colleges in kurnool. i have seen the key published in internet seems like 90% correct but answer to first question should be (A) but given as (B). You can compare the key for time being.. so tell me about yourself.. what do you do?
DeleteMY NATIVE IS HYDERABAD, WORKING AS RESEARCH WORK DEVELOPER IN GSK RD SOLUTIONS, IM CONFIDENT I WILL THROUGH IN PAPER 1 AND 2,BUT IN PAPER 3 I GOT 31 ANSWERS MATCH WITH UR KEY ,SAME 31 QUESTIONS MATCH IN OTHER KEY WHICH IS PUBLISHED IN INTERNET.
ReplyDelete--- SUNILKUMAR
Sunil, You may get around 40 questions correct but i am expecting that cutoff will be 100(50 questions) marks... anyways hope for the best
Deletehi Bhanu Garu,
Deletecut off is only as follows.(http://ugcnetonline.in/ugc_net_objective_mode.php)
75 (50%) for OC,
67.5 (45%) rounded off to 68 for OBC,
60 (40%) for PH/VH/SC/ST
all the best and let us hope positive...!
Paper-I Paper-II Paper-I + Paper-II Paper-III
DeleteGEN 40 (40%) 40 (40%) 100 (50%) 90 (45%)
OBC(NCL) 35 (35%) 35 (35%) 90 (45%) 80 (40%)
SC/ST/PH/VH 35 (35%) 35 (35%) 80 (40%) 70 (35%)
This is the ugc given cut off
Hi Naik,
DeleteI think u gave previous cutoff!
After UGC introduced as 3rd paper is also objective then the cut-off is as follows
Category Minimum marks (%) to be obtained
Paper-I Paper-II Paper-III
General 40 (40%) 40 (40%) 75 (50%)
OBC (Non-creamy layer) 35 (35%) 35 (35%) 67.5 (45%) rounded off to 68
PH/VH/SC/ST 35 (35%) 35 (35%) 60 (40%)
Reference: http://ugcnetonline.in/ugc_net_objective_mode.php
Hi Bhanu Garu,
ReplyDeleteI need one suggestion about NET!
I was writing Net but i don't know how i can use these score card.
similarly, my friend sister qualified NET-lectureship in last December. what she has to do after getting NET certificate?
could u please explain?
Thank U Very Much....!
If you qualify in NET then if goverment university has any vacancy for lecturers , u can apply...
DeleteMinimum eligibility criteria for government universities is NET qualification or Ph.D
i heard from friends that there is 100% chance that u get a govt lecturer in some university
ravi, you said your friend's sister qualified in NET.. is she from computers?
NO..! She is qualified in the subject 55- Human Resource Management !
Delete(33) which of the following software metric does not depend on programming language
ReplyDelete(a) LOC ( Lines of code )
(b) Function Point
(c) member of token
(d) None
refer (33) which of the following software metric does not depend on programming language
(a) LOC ( Lines of code )
(b) Function Point
(c) member of token
(d) None
Ans:B
follow the link :http://web.itu.edu.tr/gokmen/SE-lecture-2.pdf(slide 20)
Dear Bhanu garu are you workig for the format
Hi..will update the key .. Thanks for the information
DeleteFormat means?
In question 68 if you take =4 and m=3 then C(n+m-1,m)i.e.C(6,3)=20 where as the aswer is 10????
ReplyDeletehi.. So what do you say about answer..
DeleteQ_2 Ans (b) Dependency preserving and lossless
ReplyDeleteQ_11 Length of the IPv4 header field - Hlen:4bits
Q_17 CMM level 4 is also included in Capibility Maturity Model level 5
Q_24 All of the above
Q_35 (b) (u,v)>=12, using Floyd Warshall algorithm
Q_47 confusing, plz look at page 196 on OS Concepts 8th Edn by Galvin book.
Q_50 2 bytes = 16 bits = 1 sign bits + 15 bits = 32767
Hi Deepanwita,
DeleteQ-2 .. answer is Dependency preserving but lossy because R1 Intersection R2 is null
Thanks for the valuable answeers provided.. i have updated the key.. please have a look at other previous question papers and let me know if you find any solution..
you said that Q_2> Dependency preserving but lossy because R1 Intersection R2 is null, but there is no FD between any of the attributes of R1 to any of the attributes in R2, and they both are single theme tables.
DeleteMy next point is, having a Natural Join on R1 and R2 produces R without creating any spurious tuples, then how can we say the decomposition is lossy.
The answer should be (b) Dependency preserving and loss-less.
Finally, thank you for the wonderful blog.
Great work guys...really appreciable...thanks
ReplyDeleteThanks Abhi
DeleteGreate work.
ReplyDeleteHope to continue this kind of work.
Thanks buddy
DeleteThanks buddy
Delete33)ans:B function point http://web.itu.edu.tr/gokmen/SE-lecture-2.pdf(slide 20)
Delete92)ans:B base class constructor followed by derived class
link:http://tianrunhe.wordpress.com/2012/04/13/destructor-in-base-class-needed-to-be-virtual-in-c
88)I think it is router
refer comer book TCP/IP internetworking(chapter 2 and 3) bridge is used for same underlying technology
Link state algorithm: Ans OSPF
ReplyDelete71 : Answer of Question on COSETS :
ReplyDeleteany two coset ( left or riht) will
be identical or disjoint.
(47) In pre-emtive scheduling algorithm if time quantum increases, effective turn around time
ReplyDeleteAns: varies irreular ( some time increses, some time decreses) see RR algo in galvin and
plot that shows.
One question on Hunarian assinment, I am not
ReplyDeleteto remembet that matrix.
one question on simplex algo, in a given iteration if all values are negative and one zero. what it indicate ----> alternative optima
*Hunarian assinment ===Hungarian assignment
Deleteplase send ur 3 papar omr ans key
ReplyDeleteSorry, I filled omr sheet, but it did not come proper way on corbon copy,I cannot be sure which
Deleteoption I filled. Any way, cool for me.....waiting for result...
One more question....
Neural Network is used for clustering -------- Ans: SOM
Hello,
ReplyDeleteThanks for providing the information.
Hai sir,
ReplyDeleteI want to conform one answer that is
(34) Reliability of a software depend on
I Think it is User requiremnt
Reference:sit.iitkgp.ernet.in/~dkundu/ICITRE~1.pdf
Ans: Number of errors present in s/w. (According to the given question, I confirmed with author of the paper). Reliability also depends on some other factor.....
ReplyDeleteThnks for reply sir
DeleteThis comment has been removed by the author.
DeleteWelcome..
DeleteResult will be declare on 9 Aug 12
ReplyDeleteWell, It will be good if they declare early,
Deletebut from where U got this information.
Hi all,
ReplyDeleteWhy don't we send bunch of mails to UGC support(support@ugcnetonline.in) by asking "May i know when will be june-2012 papers will available in website? duplicate copy of OMR sheet with us, we could not understand what we have to do without question paper (or) key!"
It is good idea. I think those who have prepared the questions, surely they should have the key.
ReplyDeleteUGC have to do only collect and upload the key!. It may be problem due to more than 100 subject.
( but it seems due to only UGC staff problem and it is UGC responsibility to sort out.
Hi ravi and jainath,
ReplyDeleteWE may send the mail but i donot think they will respond to our request.Instead I suggest why not each one of us recall the question numbers in particular paper 3 of which 56 questions are already discussed in this blog
hi surabhi,
Deleteyou are right,but it is an attempt to give a signal for so many people waiting for question paper. i think they will place question papers in the website very few days to next ugc-net exam or after exam.
your suggestion is good! but it is little difficult to recall the remaining questions because i think those are came from elective subjects of computer science.
QNO subject
ReplyDelete1 LOOPs
2 pipeline
3 No of minimum colors required
4 Granularity
6 Fuzzy sets intersection
15 common between programming and functional language
like wise i will send more a others ca contribute
Q10. In minimum number state in dfa, dead state not required. So answer n+1
ReplyDeleteAnswer is n+2, because DFA means deterministic, that is for every input DFA should define the state transition.
DeleteYou are right but the question is minimum state required, in minimum state we can't take dead state.
Deleteanswer is n+1 because ..que was ..minimum number of states required required to design FA..so we may ignore dead state..
Deleten+1 is the right answer... thanks
Deletecan you post paper 3 questions....
ReplyDeletePaper-2 and paper-3 questions are mixed in this post..
ReplyDeleteanswer keys are available on UGC website for june exam
ReplyDeleteHi Bhanu, How many marks are you getting in each paper.
ReplyDeleteHi ALL,
DeleteCould u please share KEy for UGC-NET June 2012 released by UGC.
UGC NET PAPer june-2012 available in ugc website.
ReplyDeletekey also.
please check continue the discussion.
UGC NET june-2012 results and final key out..!
ReplyDeletewhat about the final criteria of
ReplyDeletemarks???
final criteria marks will be available along with mark-list. let us hope with in 3 or 4 days!
Deletequalifying criteria for ugc-net june 2012 is out..................!
ReplyDeleteCategory Paper-I Paper-II Paper-III Aggregate Of all Three Papers
General 40% 40% 50% 65%
OBC(Non Creamy Layer) 35% 35% 45% 60%
SC/ST/PWD 35% 35% 40% 55%
may be with in 2 days mark list also available in ugc website.
let us hope.
hello sir, i m doing job...but i hven't enough time for prep...pls tell me,how can i prepare to myself for NET...exam...also suggest me the books...for prep...
ReplyDeletehello sir, i m doing job...but i hven't enough time for prep...pls tell me,how can i prepare to myself for NET...exam...also suggest me the books...for prep...
ReplyDeleteNET has Huge syllabus and it has 3 papers; if ur target is Lecturer-ship; even little tough task(55%, 60%, 65% previous qualified criteria) AND NET papers has very less repetitive questions; even though u can try by reading core subjects like: OS, DBMS, DS/DAA, CN, CO, SE and previous papers.
DeleteNET has Huge syllabus and it has 3 papers; if ur target is Lecturer-ship; even little tough task(55%, 60%, 65% previous qualified criteria) AND NET papers has very less repetitive questions; even though u can try by reading core subjects like: OS, DBMS, DS/DAA, CN, CO, SE and previous papers.
ReplyDeleteNET December 2012 notification came; exam on 30-december-2012.
ReplyDeleteUGC-NET supplementary results came...!
ReplyDeletecheck it once @ UGC website
Yaah..i have cleared UGC NET-june 2012 with aggregate 64.8%....
DeleteUn-Official Information:
ReplyDeleteOsmania University is busy in UGC-NET Exam.
APSET Supplementary results will be published in the first week of Jan 2013.
when will u publish the key for dec12 net
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteUGC-NET Dec 2012 is available @
ReplyDeletehttp://ugcnetdec2012.blogspot.com
This design is incredible! You most certainly know how to keep a reader entertained.
ReplyDeleteBetween your wit and your videos, I was almost moved to start my own blog (well,
almost...HaHa!) Fantastic job. I really loved what you had to
say, and more than that, how you presented it. Too cool!
My web-site diet that works